Difference between revisions of "Hacking"
m (→Utility Subsystems: added activation by pressing number keys) |
|||
| (53 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
{{Exploration links}} | {{Exploration links}} | ||
| − | '''Hacking''' is used to access | + | '''Hacking''' is used to access Container structures in [[relic and data sites]], [[Combat sites#Chemical labs|chemical labs]] as well as mission given by Agents. |
| − | == Hacking | + | == Hacking == |
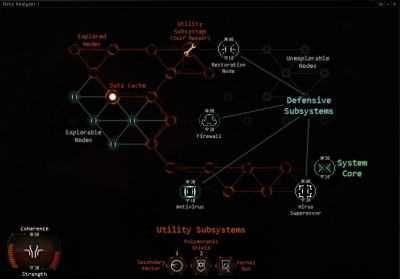
| − | [[File: | + | [[File:Hacking Indications.png|400px|thumb|The hacking mini-game with systems indications.]] |
| − | + | The goal of hacking is to '''find and disable the Container’s System Core'''. You do this by maneuvering a Virus through the board of nodes that represents the Container’s electronics. | |
| − | + | Nodes are: | |
| + | * {{Co|orange|orange}} if explored | ||
| + | * {{Co|green|green}} if adjacent to explored nodes | ||
| + | * gray if neither explored or adjacent to explored nodes | ||
| − | + | Clicking on a {{Co|green|green}} node will reveal its contents: if the node is empty, it will turn {{Co|orange|orange}} and allow you to further explore adjacent nodes. | |
| − | + | If the new node is empty it will briefly display a number between 1 and 5. The number is the distance to the nearest node with a System Core, Utility Subsystem or Data Cache. | |
| − | + | Number: | |
| − | + | * 1 means an adjacent node is a System Core, Utility Subsystem or Data Cache | |
| + | * 2, 3 and 4 means the nearest System Core, Utility Subsystem or Data Cache is respectively 2, 3 and 4 nodes away | ||
| + | * 5 means you are 5 or more nodes away from the nearest System Core, Utility Subsystem or Data Cache | ||
| − | + | The numbers 1-5 don't tell you how distant you are from the nearest Defensive Subsystem. | |
| − | + | Instead of being empty a node may contain: | |
| + | * a [[#System Core|System Core]] | ||
| + | * a [[#Defensive Subsystems|Defensive Subsystem]] | ||
| + | * a [[#Utility Subsystems|Utility Subsystem]] | ||
| + | * a [[#Data Caches|Data Cache]] | ||
| − | {|class=wikitable style="width: | + | {{Clear}} |
| + | === System Core === | ||
| + | '''Finding and disabling the System Core is the goal of hacking.''' | ||
| + | |||
| + | {|class="wikitable" style="float: right; text-align: center;" | ||
| + | |+ Difficult System Cores are defended by advanced Defensive Subsystems | ||
| + | ! scope="col" style="width: 80px;" | Difficulty | ||
| + | ! scope="col" style="width: 80px;" | System Core | ||
| + | ! scope="col" style="width: 80px;" | Firewall | ||
| + | ! scope="col" style="width: 80px;" | Anti-Virus | ||
| + | ! scope="col" style="width: 80px;" | Resto. Node | ||
| + | ! scope="col" style="width: 80px;" | Suppressor | ||
| + | |||
| + | |- | ||
| + | | style="text-align: left;" | Very Easy | ||
| + | | [[File:Core node very easy green.png]] | ||
| + | | [[File:Firewall node easy.png]] | ||
| + | | [[File:Antivirus node easy.png]] | ||
| + | | [[image:Icon_large_red_x.png]] | ||
| + | | [[image:Icon_large_red_x.png]] | ||
| + | |||
| + | |- | ||
| + | | style="text-align: left;" | Easy | ||
| + | | [[File:Core node easy green.png]] | ||
| + | | [[File:Firewall_node.png]] | ||
| + | | [[File:Antivirus node easy.png]] | ||
| + | | [[image:Icon_large_red_x.png]] | ||
| + | | [[image:Icon_large_red_x.png]] | ||
| + | |||
| + | |- | ||
| + | | style="text-align: left;" | Medium | ||
| + | | [[File:Core node_medium orange.png]] | ||
| + | | [[File:Firewall node medium.png]] | ||
| + | | [[File:Antivirus_node.png]] | ||
| + | | [[File:Restorer_node.png]] | ||
| + | | [[image:Icon_large_red_x.png]] | ||
| + | |||
| + | |- | ||
| + | | style="text-align: left;" | Hard | ||
| + | | [[File:Core node hard red.png]] | ||
| + | | [[File:Firewall hard node.png]] | ||
| + | | [[File:Antivirus hard node.png]] | ||
| + | | [[File:Restorer node.png]] | ||
| + | | [[File:Supressor node.png]] | ||
| + | |} | ||
| + | |||
| + | System Cores, Defensive Subsystems and your Virus have: | ||
| + | * '''Coherence''' ([[File:Hacking coherence.png]]) which is their health | ||
| + | * '''Strength''' ([[File:Hacking strength.png]]) which is their attack power | ||
| + | |||
| + | When you click on the System Core or Defensive Subsystem your Virus will attack. Attacking is turn-based: | ||
| + | # your Virus attacks, lowering the System's Coherence by your Virus Strength and then | ||
| + | # the System Core or Defensive Subsystem retaliates if it survived the attack | ||
| + | |||
| + | When you reduce the System's Coherence to 0, it is disabled and removed from the board. | ||
| + | |||
| + | You fail a hack when: | ||
| + | * your Virus Coherence reaches 0 | ||
| + | * close the hacking window for any reason such as moving too far away from the Container structure | ||
| + | |||
| + | If you fail the hack: | ||
| + | * twice a Data or Relic Site Container structure will be destroyed | ||
| + | * once a Covert Research Facility Container structure will be destroyed and deal a large amount of damage to all ships in range | ||
| + | * once a Sleeper Cache will release a deadly toxic gas, activate turrets or put up other obstacle | ||
| + | |||
| + | {{Clear}} | ||
| + | === Defensive Subsystems === | ||
| + | '''Defensive Subsystems prevent you from exploring adjacent nodes until they are disabled.''' | ||
| + | |||
| + | {|class="wikitable" style="width: 900px;" | ||
|- | |- | ||
|[[File:Firewall_node.png]] | |[[File:Firewall_node.png]] | ||
| − | |'''Firewalls''' have high | + | |'''Firewalls''' have high Coherence and low Strength. |
| + | |||
|- | |- | ||
| + | |[[File:Antivirus_node.png]] | ||
| + | |'''Anti-Virus''' have low Coherence, but high Strength. | ||
| − | |||
| − | |||
|- | |- | ||
| + | |[[File:Restorer_node.png]] | ||
| + | |'''Restoration Nodes''' give 20 extra Coherence to a random Defensive Subsystem at the end of each turn. They are a high priority target. | ||
| − | |||
| − | |||
|- | |- | ||
| − | |||
|[[File:Supressor_node.png]] | |[[File:Supressor_node.png]] | ||
| − | |'''Virus | + | |'''Virus Suppressors''' lower your Virus Strength by 15. Your Virus Strength cannot go below 10. They are a high priority target. |
| − | |||
| − | |||
| − | |||
|} | |} | ||
| − | === | + | === Utility Subsystems === |
| − | + | '''Utility Subsystems''' assist you in disabling the System Core and Defensive Subsystems. | |
| − | + | When you click the Utility Subsystem it will be added to a free utility slot. | |
| − | |||
| − | Utility | + | Activate the Utility Subsystem by clicking on it in your utility belt. They can also be activated by pressing the number keys "1", "2" etc. The number of utility belt slots depends on your Analyzer module. |
| − | {|class=wikitable style="width: 900px;background:#111111" | + | {|class="wikitable" style="width: 900px;background:#111111" |
|- | |- | ||
|[[File:Self_repair2.png]] | |[[File:Self_repair2.png]] | ||
| − | |'''Self | + | |'''Self Repairs''' increase your Virus Coherence by 5-10 each turn for the three turns. Use it immediately as your Virus doesn't have a maximum Coherence value. |
| + | |||
|- | |- | ||
| + | |[[File:Kernel_rot2.png]] | ||
| + | |'''Kernel Rots''' reduce a System’s Coherence by 50%. Use it on high Coherence Systems. | ||
| − | |||
| − | |||
|- | |- | ||
| + | |[[File:Polymorphic_shield.png]] | ||
| + | |'''Polymorphic Shields''' nullify the next two System attacks against your Virus. Use it before attacking high Strength Systems. | ||
| − | |||
| − | |||
|- | |- | ||
| + | |[[File:Secondary_vector2.png]] | ||
| + | |'''Secondary Vectors''' reduce a System’s Coherence by 20 each turn for three turns. Use it against a Suppressor Defensive Subsystem. | ||
| − | | | + | |} |
| − | | | + | |
| + | === Data Caches === | ||
| + | {|class="wikitable" | ||
|- | |- | ||
| − | + | |[[File:Data cache2.png]] | |
| + | |'''Data Caches''' can contain either a Defensive or Utility Subsystem. | ||
| + | |||
|} | |} | ||
| − | + | Data Caches have a 50-50 probability of containing a Defensive or a Utility Subsystem. | |
| + | |||
| + | Open a Data Cache by clicking on it. Open them only as a last resort. | ||
== Skills == | == Skills == | ||
| − | |||
* {{sk|Archaeology|price=yes|mult=yes}}: Required skill for the use of Relic Analyzer modules. Gives +10 Virus Coherence per level. | * {{sk|Archaeology|price=yes|mult=yes}}: Required skill for the use of Relic Analyzer modules. Gives +10 Virus Coherence per level. | ||
| − | ** Relic Analyzers require Archaeology, and are a fairly cheap mid-slot module used to interact with structures | + | ** Relic Analyzers require Archaeology, and are a fairly cheap mid-slot module used to interact with Container structures. A good amount of your income as an explorer will come from accessing these Container structures, so note this skill's importance! |
| − | ** Higher skill levels | + | ** Higher skill levels makes hacking Relic Site Container structures easier, with {{sk|Archaeology|V}} allowing you to use the powerful Relic Analyzer II module. Explorers should considering training Archaeology to V, especially if they intend to hack Relic Sites in NullSec or Wormholes. |
* {{sk|Hacking|price=yes|mult=yes}}: Required skill for the use of Data Analyzer modules. Gives +10 Virus Coherence per level. | * {{sk|Hacking|price=yes|mult=yes}}: Required skill for the use of Data Analyzer modules. Gives +10 Virus Coherence per level. | ||
| − | ** ''A la'' Archaeology, Data Analyzers require Hacking, and open structures found in Data Sites. {{sk|Hacking|I}} has slightly higher requirements than Archaeology I, but make sure you get both skills, so that you can hack any sites you find. | + | ** ''A la'' Archaeology, Data Analyzers require Hacking, and open Container structures found in Data Sites, Chemical Labs and Ghost Sites. {{sk|Hacking|I}} has slightly higher requirements than Archaeology I, but make sure you get both skills, so that you can hack any sites you find. |
| − | ** Also like Archaeology, higher skill levels make | + | ** Also like Archaeology, higher skill levels make hacking easier, and {{sk|Hacking|V}} will give you access to the Data Analyzer II module, which gives better bonuses, and is needed for Data Sites in NullSec or Wormholes. |
| − | ==Ships and equipment== | + | == Ships and equipment == |
| − | ===Ships=== | + | === Ships === |
| − | Hacking can be done in any ship that has mid slots for Data and/or Relic Analyzers. However, | + | Hacking can be done in any ship that has mid slots for Data and/or Relic Analyzers. However, exploration ships have a role bonus for both Virus and scan Strength. |
| − | Each | + | Each Empire's Tech 1 Exploration Frigate has a role bonus of +5 Virus Strength to both Data and Relic Analyzers. These ships also get an 7.5% (37.5% max) increase to scan strength per racial frigate level, which helps in scanning down Cosmic Signatures. |
* {{sh|Magnate}} | * {{sh|Magnate}} | ||
| Line 93: | Line 175: | ||
* {{sh|Probe}} | * {{sh|Probe}} | ||
| − | + | Covert Operation ships are the direct upgrade from Tech 1 Exploration Frigates. They get a +10 bonus to Virus Strength, +10% (50% max) per level bonus to scanning, and can use Covert Ops Cloaking Device II. | |
* {{sh|Anathema}} | * {{sh|Anathema}} | ||
| Line 99: | Line 181: | ||
* {{sh|Helios}} | * {{sh|Helios}} | ||
* {{sh|Cheetah}} | * {{sh|Cheetah}} | ||
| + | * {{sh|Pacifier}} | ||
| + | |||
| + | The [[Sisters of EVE]] faction ships all have a +10 bonus to Virus Strength, a 37.5% role bonus to scanning, and both the Astero and the Stratios can use a Covert Ops Cloaking Device II. They also get bonus to armor resists, energy turrets and drones making them capable combat crafts. They have lower skill requirements than Covert Operation ships, but they are more expensive than Covert Operation ships. | ||
| − | |||
* {{sh|Astero}} Frigate. (CPU is low, making it hard to fit an Expanded Probe Launcher.) | * {{sh|Astero}} Frigate. (CPU is low, making it hard to fit an Expanded Probe Launcher.) | ||
* {{sh|Stratios}} Cruiser. | * {{sh|Stratios}} Cruiser. | ||
| − | * {{sh|Nestor}} Battleship. Role Bonus: 50% bonus to Core and Combat Scanner Probe strength. Cannot fit a Covert Ops | + | * {{sh|Nestor}} Battleship. Role Bonus: 50% bonus to Core and Combat Scanner Probe strength. Cannot fit a Covert Ops Cloaking Device II. |
| − | [[ | + | [[Strategic Cruisers|Strategic cruisers]] can be fitted with the '''Covert Reconfiguration''' subsystem that gives them 10% per level scan bonus, +10 Virus Strength, and the ability to use Covert Ops Cloaking Device II. Strategic cruisers are very expensive ships. |
* {{sh|Legion}} | * {{sh|Legion}} | ||
| Line 112: | Line 196: | ||
* {{sh|Loki}} | * {{sh|Loki}} | ||
| − | ===Ship equipment=== | + | === Ship equipment === |
| − | + | Data Analyzer or Relic Analyzer allow you to hack Data and Relic Sites. There is no additional high, mid or low slot equipment to make hacking easier. | |
Full list of normally used scanning equipment: | Full list of normally used scanning equipment: | ||
| − | {|class=wikitable style="width: 900px; | + | {|class="wikitable" style="width: 900px;" |
|- | |- | ||
| − | |[[File:Icon data analyzer i.png|link=|]] | + | | [[File:Icon data analyzer i.png|link=|]] |
| − | |'''Data Analyzers''' are used to hack [[ | + | | '''Data Analyzers''' are used to hack [[Relic and data sites|Data]] and [[Combat sites#Chemical Labs|Chemical Lab]] sites found while exploring. |
The T1 module has a base 40 Virus Coherence and 20 Strength, with the T2 Version has an additional +20 Virus Coherence (60 total) and +10 Virus Strength (30 total) | The T1 module has a base 40 Virus Coherence and 20 Strength, with the T2 Version has an additional +20 Virus Coherence (60 total) and +10 Virus Strength (30 total) | ||
|- | |- | ||
| − | |[[File:Icon relic analyzer.png|link=|]] | + | | [[File:Icon relic analyzer.png|link=|]] |
| − | |'''Relic Analyzers''' are only used to hack [[ | + | | '''Relic Analyzers''' are only used to hack [[Relic and data sites|Relic]] Sites |
The T1 module has a base 40 Virus Coherence and 20 Strength, with the T2 Version has an additional +20 Virus Coherence (60 total) and +10 Virus Strength (30 total) | The T1 module has a base 40 Virus Coherence and 20 Strength, with the T2 Version has an additional +20 Virus Coherence (60 total) and +10 Virus Strength (30 total) | ||
|- | |- | ||
| − | |[[File:IntegratedAnalyzer.png|link=|]] | + | | [[File:IntegratedAnalyzer.png|link=|]] |
| − | |'''Integrated Analyzers''' are | + | | '''Integrated Analyzers''' are modules that can hack both [[Relic and data sites|Data and Relic]] sites. They are more expensive then their specialized counterparts, have lower Virus Coherence and Strength, and smaller utility belt slots. |
| − | Integrated Analyzers | + | Integrated Analyzers get bonus Coherence from both Archaeology and Hacking skills as well as rigs and implants. |
|- | |- | ||
| − | |[[File:Icon rig CPU.png|link=|]] | + | | [[File:Icon rig CPU.png|link=|]] |
| − | |'''Memetic Algorithm Bank''' rig increases the | + | | '''Memetic Algorithm Bank''' rig increases the Virus Coherence of both Data and Integrated Analyzers. The T1 rig increases the Coherence by +10, and the T2 version increases it by +20. Due to Calibration size and ISK cost, it is more cost-effective to have two T1 rigs than one T2 rig. |
|- | |- | ||
| − | |[[File:Icon rig CPU.png|link=|]] | + | | [[File:Icon rig CPU.png|link=|]] |
| − | |'''Emission Scope Sharpener''' rig increases the | + | | '''Emission Scope Sharpener''' rig increases the Virus Coherence of both Relic and Integrated Analyzers. The T1 rig increases the Coherence by +10, and the T2 version increases it by +20. Due to Calibration size and ISK cost, it is more cost-effective to have two T1 rigs than one T2 rig. |
|} | |} | ||
| − | + | The slot 9 implants that improve Virus Coherence and Strength. | |
{| class="wikitable" | {| class="wikitable" | ||
| − | |- | + | |- style="background: #222222;" |
| − | + | ! Implant | |
| − | ! | + | ! Effect |
|- | |- | ||
| − | |Poteque 'Prospector' Archaeology AC-905 | + | | Poteque 'Prospector' Archaeology AC-905 |
| − | | +5 | + | | +5 Virus Coherence for Relic and Integrated Analyzers |
|- | |- | ||
| − | |Poteque 'Prospector' Hacking HC-905 | + | | Poteque 'Prospector' Hacking HC-905 |
| − | | +5 | + | | +5 Virus Coherence for Data and Integrated Analyzers |
|- | |- | ||
| − | |Neural Lace 'Blackglass' Net Intrusion 920-40 | + | | Neural Lace 'Blackglass' Net Intrusion 920-40 |
| − | | -40 | + | | -40 Virus Coherence and +20 Virus Strength for Data and Integrated Analyzers |
|} | |} | ||
| − | The slot 10 EY-1005 implant improves | + | The slot 10 EY-1005 implant improves Virus Coherence. |
{| class="wikitable" | {| class="wikitable" | ||
| − | |- | + | |- style="background: #222222;" |
| − | + | ! Implant | |
| − | ! | + | ! Effect |
|- | |- | ||
| − | |Poteque 'Prospector' Environmental Analysis EY-1005 | + | | Poteque 'Prospector' Environmental Analysis EY-1005 |
| − | | +5 coherence for | + | | +5 coherence for Data, Relic and Integrated analyzers |
|} | |} | ||
== Tips and Tricks == | == Tips and Tricks == | ||
| − | * | + | * '''Explore the board as much as possible before attacking a Defensive Subsystem.''' You may just stumble onto the System Core early! Restoration Nodes and Virus Suppressors are the exception to this though, as they should be removed from the board as soon as possible. |
* '''Always pick up Utility Subsystems as soon as they are exposed.''' If you keep exploring without snagging these, a Defensive Subsystem might pop up and cut off your access to them! | * '''Always pick up Utility Subsystems as soon as they are exposed.''' If you keep exploring without snagging these, a Defensive Subsystem might pop up and cut off your access to them! | ||
| − | * '''Always use a Self Repair as soon as you find it.''' | + | * '''Always use a Self Repair as soon as you find it.''' It increases your Virus Coherence, so there is no gain in waiting. |
* '''Don’t open Data Caches until you’ve fully explored all their adjacent nodes.''' You don’t want your exploration to be cut off by an unexpected Defensive Subsystem! | * '''Don’t open Data Caches until you’ve fully explored all their adjacent nodes.''' You don’t want your exploration to be cut off by an unexpected Defensive Subsystem! | ||
| − | ** | + | ** Difficult hack's Data Caches might expose Restoration Nodes and Suppressors. '''Leave opening Data Caches as a last resort.''' |
| − | + | * '''Use the 1-5 numbers to guide your movement''' around the board. For example, if you're approaching an edge or corner of the grid, and the number 5 shows up, then trying to explore anything towards that corner/edge is not useful, because you know that there cannot be anything good within 5 nodes. In general, you want to click in directions that make the numbers smaller. Because the numbers disappear as you move along, you need to remember where there were 5's, so you know which areas not to bother going back to later. | |
| − | * '''Use the 1-5 | ||
* '''Use the Rule of Six'''. This rule is slightly complicated, but can make your life when hacking much easier. The rule is that if you have a node that has six edges leading away from it ( a "complete" node with no missing nodes in the hexagon around it), then that node is guaranteed to 1) Have no Defensive Subsystems in it OR 2) be adjacent to the System Core. What that means in practice is that you can use these squares to move safely through the board, and any Defensive Subsystems you find tell you where the System Core is. It is usually worthwhile to try to reach and use areas of the map with many of these "complete" nodes when hacking. You can find a video tutorial [https://www.youtube.com/watch?v=h5uQC74VvVQ here]. | * '''Use the Rule of Six'''. This rule is slightly complicated, but can make your life when hacking much easier. The rule is that if you have a node that has six edges leading away from it ( a "complete" node with no missing nodes in the hexagon around it), then that node is guaranteed to 1) Have no Defensive Subsystems in it OR 2) be adjacent to the System Core. What that means in practice is that you can use these squares to move safely through the board, and any Defensive Subsystems you find tell you where the System Core is. It is usually worthwhile to try to reach and use areas of the map with many of these "complete" nodes when hacking. You can find a video tutorial [https://www.youtube.com/watch?v=h5uQC74VvVQ here]. | ||
[[Category:Exploration]] | [[Category:Exploration]] | ||
Latest revision as of 09:51, 29 May 2023

|
| Exploration |
|---|
| Site types |
| Guides |
Hacking is used to access Container structures in relic and data sites, chemical labs as well as mission given by Agents.
Contents
Hacking
The goal of hacking is to find and disable the Container’s System Core. You do this by maneuvering a Virus through the board of nodes that represents the Container’s electronics.
Nodes are:
- orange if explored
- green if adjacent to explored nodes
- gray if neither explored or adjacent to explored nodes
Clicking on a green node will reveal its contents: if the node is empty, it will turn orange and allow you to further explore adjacent nodes.
If the new node is empty it will briefly display a number between 1 and 5. The number is the distance to the nearest node with a System Core, Utility Subsystem or Data Cache.
Number:
- 1 means an adjacent node is a System Core, Utility Subsystem or Data Cache
- 2, 3 and 4 means the nearest System Core, Utility Subsystem or Data Cache is respectively 2, 3 and 4 nodes away
- 5 means you are 5 or more nodes away from the nearest System Core, Utility Subsystem or Data Cache
The numbers 1-5 don't tell you how distant you are from the nearest Defensive Subsystem.
Instead of being empty a node may contain:
System Core
Finding and disabling the System Core is the goal of hacking.
| Difficulty | System Core | Firewall | Anti-Virus | Resto. Node | Suppressor |
|---|---|---|---|---|---|
| Very Easy | 
|

|

|
||
| Easy | 
|

|

|
||
| Medium | 
|

|

|

|
|
| Hard | 
|

|

|

|

|
System Cores, Defensive Subsystems and your Virus have:
When you click on the System Core or Defensive Subsystem your Virus will attack. Attacking is turn-based:
- your Virus attacks, lowering the System's Coherence by your Virus Strength and then
- the System Core or Defensive Subsystem retaliates if it survived the attack
When you reduce the System's Coherence to 0, it is disabled and removed from the board.
You fail a hack when:
- your Virus Coherence reaches 0
- close the hacking window for any reason such as moving too far away from the Container structure
If you fail the hack:
- twice a Data or Relic Site Container structure will be destroyed
- once a Covert Research Facility Container structure will be destroyed and deal a large amount of damage to all ships in range
- once a Sleeper Cache will release a deadly toxic gas, activate turrets or put up other obstacle
Defensive Subsystems
Defensive Subsystems prevent you from exploring adjacent nodes until they are disabled.
Utility Subsystems
Utility Subsystems assist you in disabling the System Core and Defensive Subsystems.
When you click the Utility Subsystem it will be added to a free utility slot.
Activate the Utility Subsystem by clicking on it in your utility belt. They can also be activated by pressing the number keys "1", "2" etc. The number of utility belt slots depends on your Analyzer module.
Data Caches

|
Data Caches can contain either a Defensive or Utility Subsystem. |
Data Caches have a 50-50 probability of containing a Defensive or a Utility Subsystem.
Open a Data Cache by clicking on it. Open them only as a last resort.
Skills
- Archaeology (3x, 250k ISK): Required skill for the use of Relic Analyzer modules. Gives +10 Virus Coherence per level.
- Relic Analyzers require Archaeology, and are a fairly cheap mid-slot module used to interact with Container structures. A good amount of your income as an explorer will come from accessing these Container structures, so note this skill's importance!
- Higher skill levels makes hacking Relic Site Container structures easier, with Archaeology V allowing you to use the powerful Relic Analyzer II module. Explorers should considering training Archaeology to V, especially if they intend to hack Relic Sites in NullSec or Wormholes.
- Hacking (3x, 250k ISK): Required skill for the use of Data Analyzer modules. Gives +10 Virus Coherence per level.
- A la Archaeology, Data Analyzers require Hacking, and open Container structures found in Data Sites, Chemical Labs and Ghost Sites. Hacking I has slightly higher requirements than Archaeology I, but make sure you get both skills, so that you can hack any sites you find.
- Also like Archaeology, higher skill levels make hacking easier, and Hacking V will give you access to the Data Analyzer II module, which gives better bonuses, and is needed for Data Sites in NullSec or Wormholes.
Ships and equipment
Ships
Hacking can be done in any ship that has mid slots for Data and/or Relic Analyzers. However, exploration ships have a role bonus for both Virus and scan Strength.
Each Empire's Tech 1 Exploration Frigate has a role bonus of +5 Virus Strength to both Data and Relic Analyzers. These ships also get an 7.5% (37.5% max) increase to scan strength per racial frigate level, which helps in scanning down Cosmic Signatures.
Covert Operation ships are the direct upgrade from Tech 1 Exploration Frigates. They get a +10 bonus to Virus Strength, +10% (50% max) per level bonus to scanning, and can use Covert Ops Cloaking Device II.
The Sisters of EVE faction ships all have a +10 bonus to Virus Strength, a 37.5% role bonus to scanning, and both the Astero and the Stratios can use a Covert Ops Cloaking Device II. They also get bonus to armor resists, energy turrets and drones making them capable combat crafts. They have lower skill requirements than Covert Operation ships, but they are more expensive than Covert Operation ships.
 Astero Frigate. (CPU is low, making it hard to fit an Expanded Probe Launcher.)
Astero Frigate. (CPU is low, making it hard to fit an Expanded Probe Launcher.) Stratios Cruiser.
Stratios Cruiser. Nestor Battleship. Role Bonus: 50% bonus to Core and Combat Scanner Probe strength. Cannot fit a Covert Ops Cloaking Device II.
Nestor Battleship. Role Bonus: 50% bonus to Core and Combat Scanner Probe strength. Cannot fit a Covert Ops Cloaking Device II.
Strategic cruisers can be fitted with the Covert Reconfiguration subsystem that gives them 10% per level scan bonus, +10 Virus Strength, and the ability to use Covert Ops Cloaking Device II. Strategic cruisers are very expensive ships.
Ship equipment
Data Analyzer or Relic Analyzer allow you to hack Data and Relic Sites. There is no additional high, mid or low slot equipment to make hacking easier.
Full list of normally used scanning equipment:
| Data Analyzers are used to hack Data and Chemical Lab sites found while exploring.
The T1 module has a base 40 Virus Coherence and 20 Strength, with the T2 Version has an additional +20 Virus Coherence (60 total) and +10 Virus Strength (30 total) | |
| Relic Analyzers are only used to hack Relic Sites
The T1 module has a base 40 Virus Coherence and 20 Strength, with the T2 Version has an additional +20 Virus Coherence (60 total) and +10 Virus Strength (30 total) | |

|
Integrated Analyzers are modules that can hack both Data and Relic sites. They are more expensive then their specialized counterparts, have lower Virus Coherence and Strength, and smaller utility belt slots.
Integrated Analyzers get bonus Coherence from both Archaeology and Hacking skills as well as rigs and implants. |
| Memetic Algorithm Bank rig increases the Virus Coherence of both Data and Integrated Analyzers. The T1 rig increases the Coherence by +10, and the T2 version increases it by +20. Due to Calibration size and ISK cost, it is more cost-effective to have two T1 rigs than one T2 rig. | |
| Emission Scope Sharpener rig increases the Virus Coherence of both Relic and Integrated Analyzers. The T1 rig increases the Coherence by +10, and the T2 version increases it by +20. Due to Calibration size and ISK cost, it is more cost-effective to have two T1 rigs than one T2 rig. |
The slot 9 implants that improve Virus Coherence and Strength.
| Implant | Effect |
|---|---|
| Poteque 'Prospector' Archaeology AC-905 | +5 Virus Coherence for Relic and Integrated Analyzers |
| Poteque 'Prospector' Hacking HC-905 | +5 Virus Coherence for Data and Integrated Analyzers |
| Neural Lace 'Blackglass' Net Intrusion 920-40 | -40 Virus Coherence and +20 Virus Strength for Data and Integrated Analyzers |
The slot 10 EY-1005 implant improves Virus Coherence.
| Implant | Effect |
|---|---|
| Poteque 'Prospector' Environmental Analysis EY-1005 | +5 coherence for Data, Relic and Integrated analyzers |
Tips and Tricks
- Explore the board as much as possible before attacking a Defensive Subsystem. You may just stumble onto the System Core early! Restoration Nodes and Virus Suppressors are the exception to this though, as they should be removed from the board as soon as possible.
- Always pick up Utility Subsystems as soon as they are exposed. If you keep exploring without snagging these, a Defensive Subsystem might pop up and cut off your access to them!
- Always use a Self Repair as soon as you find it. It increases your Virus Coherence, so there is no gain in waiting.
- Don’t open Data Caches until you’ve fully explored all their adjacent nodes. You don’t want your exploration to be cut off by an unexpected Defensive Subsystem!
- Difficult hack's Data Caches might expose Restoration Nodes and Suppressors. Leave opening Data Caches as a last resort.
- Use the 1-5 numbers to guide your movement around the board. For example, if you're approaching an edge or corner of the grid, and the number 5 shows up, then trying to explore anything towards that corner/edge is not useful, because you know that there cannot be anything good within 5 nodes. In general, you want to click in directions that make the numbers smaller. Because the numbers disappear as you move along, you need to remember where there were 5's, so you know which areas not to bother going back to later.
- Use the Rule of Six. This rule is slightly complicated, but can make your life when hacking much easier. The rule is that if you have a node that has six edges leading away from it ( a "complete" node with no missing nodes in the hexagon around it), then that node is guaranteed to 1) Have no Defensive Subsystems in it OR 2) be adjacent to the System Core. What that means in practice is that you can use these squares to move safely through the board, and any Defensive Subsystems you find tell you where the System Core is. It is usually worthwhile to try to reach and use areas of the map with many of these "complete" nodes when hacking. You can find a video tutorial here.