Difference between revisions of "Relic and data sites"
m (→Sleeper caches) |
(Moved hacking info here) |
||
| Line 6: | Line 6: | ||
* Drone data sites | * Drone data sites | ||
* Ghost sites | * Ghost sites | ||
| − | * Sleeper caches | + | * Sleeper caches |
| + | * Sleeper sites. | ||
==Pirate sites== | ==Pirate sites== | ||
| Line 77: | Line 78: | ||
Note: The author of this section did model all 4 frigates in [[EFT]], using a damage control I + explosive deflection field I + small shield extender I (except for the Magnate, as noted) and with the "without skills" option, and got just over 2k (Imicus) to 2.7k (Heron with 1 EDF) shield ehp vs. explosive damage on all the above ships except the armor-tanked magnate (which had about 2.5k shield+armor ehp vs. explosive, with AEH+100mm plates+DC+EANM). However, TEST YOUR OWN FIT with a fitting tool and/or calculate your [[EHP]] vs. explosive damage before you go blow yourself up. Remember to repair any armor/hull damage you may have suffered afterwards (as noted, this should only be necessary with the Magnate). | Note: The author of this section did model all 4 frigates in [[EFT]], using a damage control I + explosive deflection field I + small shield extender I (except for the Magnate, as noted) and with the "without skills" option, and got just over 2k (Imicus) to 2.7k (Heron with 1 EDF) shield ehp vs. explosive damage on all the above ships except the armor-tanked magnate (which had about 2.5k shield+armor ehp vs. explosive, with AEH+100mm plates+DC+EANM). However, TEST YOUR OWN FIT with a fitting tool and/or calculate your [[EHP]] vs. explosive damage before you go blow yourself up. Remember to repair any armor/hull damage you may have suffered afterwards (as noted, this should only be necessary with the Magnate). | ||
| − | ==Tips and tricks== | + | ==Hacking== |
| + | |||
| + | Mercifully, the hacking minigame is identical in both Data and Relic Sites, aside from a few cosmetic changes to the game’s playfield and sound effects. The object of the hacking minigame is to '''find and disable the container’s System Core'''. You do this by maneuvering a virus through the board of “nodes” that represent the container’s electronics. | ||
| + | |||
| + | Moving around the board is easy enough. Unexplored nodes in the system are marked as green. Clicking on an unexplored node will reveal its contents: if the node is empty, it will turn orange and allow you to further explore nodes adjacent to it. Sometimes, however, a node will contain an obstacle or other item of interest. | ||
| + | |||
| + | Additionally, as you click on each node, if it is unoccupied (or after you clear the item from the node), it will briefly display a "minesweeper" number, from 1 to 5, which indicates the distance from the nearest non-empy node (5 means "5 or more".). This shows distance from any undiscovered Utility Subsystem, System Core, or Data Cache. The numbers can be used to guide the direction that you should move around the grid. | ||
| + | |||
| + | Among the various things a node may contain are... | ||
| + | |||
| + | ===Defensive Subsystems=== | ||
| + | These are represented by large circles with an icon inside, and they will be the bane of your hacking existence. '''Defensive Subsystems prevent you from exploring adjacent nodes until they are disabled.''' Each Defensive Subsystem has two ratings: '''Coherence''' represented by an asterisk atop the Subsystem, which is the equivalent of its health/HP, and '''Strength''' represented by a “wifi/signal” icon listed at the bottom of the Subsystem, which is equivalent to its “attack power.” | ||
| + | |||
| + | Your virus has a Coherence and Strength, too, which you can use to disable the system’s defenses! Your virus’s Coherence and Strength are listed in the bottom left of the hacking window. You can attack a Defensive Subsystem by clicking it after it has been explored. Attacking a Subsystem is turn-based: your virus will attack the Subsystem lowering the subsystem's Coherence by your Virus Strength, and then, ''if the Subsystem is still active'', it will attack your virus back. If you reduce the subsystem's Coherence to 0, it is disabled and removed from the board. | ||
| + | |||
| + | If your Virus Coherence reaches 0, you fail the hack and the window is closed. Failing a hack '''once''' does not matter for regular Data/Relic sites, but failing a second hack will destroy that container. (Note that for some special kinds of containers/sites, such as [[Ghost Site|Ghost Sites]], Sleeper Caches, etc., failing the first hack might cause an explosion, or have other negative effects.). Interrupting a hack counts as a failure, and that includes moving too far away from the can (out of range of your analyzer) while the hacking window is open. This is sometimes a problem for frigates with a MicroWarpDrive active, where you can overshoot the can when Approaching it too fast - so be careful. | ||
| + | |||
| + | * Defensive Subsystems come in a few different types. | ||
| + | ** '''Firewalls''' have high coherence, but low strength. | ||
| + | ** '''Anti-Virus''' subsystems have low coherence, but high strength. | ||
| + | ** '''Restoration Nodes''' show up in more difficult hacks. Each turn they are active, they will give extra coherence to '''all''' other uncovered defensive subsystems. Incredibly nasty. | ||
| + | ** '''Virus Suppressor''' subsystems lower your Virus Strength while active. | ||
| + | |||
| + | [[File:Hacking_Indications.png|400px|thumb|right|The hacking minigame with systems indications.]] | ||
| + | |||
| + | ===System Core=== | ||
| + | The System Core operates a lot like a Defensive Subsystem, with the major difference that '''disabling it will successfully complete the hack'''. Its icon looks like a “><” inside a Subsystem circle. | ||
| + | * The color of the System Core reflects the difficulty of the container: Green for easy; Orange for medium; Red for hard. | ||
| + | |||
| + | ===Data Caches=== | ||
| + | Data Caches act a bit like a “treasure chest.” They can contain either a “treasure” (a useful Utility Subsystem), or a “trap” (a particularly nasty Defensive Subsystem). Data Caches have to be manually opened after being exposed (single-click them), so you can safely leave the decision as to whether or not to chance their activation until later on in your hacking attempt. | ||
| + | |||
| + | ===Utility Subsystem=== | ||
| + | Utility Subsystems are helpful, consumable “files” that have been left inside the system. You can click one once it has been exposed to add it to a utility slot at the bottom middle of your hacking window. They can then be used by clicking the appropriate utility slot. You can only store three Utility Subsystems at a time, so plan ahead! | ||
| + | |||
| + | * Utility Subsystems are extremely useful and come in a few different types. | ||
| + | ** '''Self Repair''' utilities increase your Virus Coherence by a variable amount. A single Self Repair has three “charges”: the first is consumed immediately after use, and the next two are automatically used after your next two actions in the system (i.e., exploring a node, attacking a subsystem). Always use a Self Repair as soon as you find it - there is no gain in waiting. | ||
| + | ** '''Kernel Rot''' utilities reduces a target subsystem’s Coherence by 50%. Great for use on the System Core. Useful too on defensive subsystems with high Coherence. | ||
| + | ** '''Secondary Vector''' utilities reduces a target’s Coherence by a variable amount. Much like the Self Repair utility, the Secondary Vector has three charges: one used immediately, and two more that fire off after taking actions. | ||
| + | ** '''Polymorphic Shield''' utilities prevent the next two instances of damage done to your virus. Good for taking down subsystems with high Strength. | ||
| + | |||
| + | Thankfully, exploring until you find the System Core and then annihilating it isn’t too difficult in the vast majority of sites you will find in high-sec. With a little practice, you’ll be hacking with the best of them! | ||
| + | |||
| + | === Hacking Tips and Tricks === | ||
| + | * As a general rule, '''you’ll want to explore as many nodes as you can before attacking any static Defensive Subsystems.''' In general, it’s better to explore the entire board before engaging with any subsystems: you may just stumble onto the System Core early! Restoration Nodes and Virus Suppressors are the exception to this though, as they should be removed from the board as soon as possible. | ||
| + | * '''Always pick up Utility Subsystems as soon as they are exposed.''' If you keep exploring without snagging these, a Defensive Subsystem might pop up and cut off your access to them! | ||
| + | * '''Always use a Self Repair as soon as you find it.''' It simply increases your Coherence, so there is no gain in waiting. | ||
| + | * '''Don’t open Data Caches until you’ve fully explored all their adjacent nodes.''' You don’t want your exploration to be cut off by an unexpected Defensive Subsystem! | ||
| + | ** Additionally, more difficult hacks contain Data Caches that might expose particularly nasty Defensive Subsystems (Restoration Nodes), so sometimes, '''you may just want to leave opening Data Caches as a last resort.''' | ||
| + | * Because exposed Defensive Subsystems cut off access to adjacent nodes, '''you may want to explore nodes along the edges first before exploring inward'''. This is because if you happen to expose a Firewall or Anti-Virus along a “wall,” you will be a bit less likely to cut off all of your movement options in that direction. | ||
| + | * '''Use the 1-5 "minesweeper" numbers to guide your movement''' around the grid. For example, if you're approaching an edge or corner of the grid, and the number is a 5, then trying to explore anything towards that corner/edge is not useful, because you know that there cannot be anything good within 5 nodes. In general, you want to click in directions that make the numbers smaller. Because the numbers disappear as you move along, you need to remember where there were 5's, so you know which areas not to bother going back to later. | ||
| + | |||
| + | ==General tips and tricks== | ||
* The contents of containers can be scanned with cargo scanners before hacking. This allows skipping containers that do not have valuable contents. | * The contents of containers can be scanned with cargo scanners before hacking. This allows skipping containers that do not have valuable contents. | ||
* Emptied sites will despawn in few minutes. Sites that have been warped to or partially completed will despawn in few hours. | * Emptied sites will despawn in few minutes. Sites that have been warped to or partially completed will despawn in few hours. | ||
Revision as of 10:59, 22 April 2017
Reason: Needs more accurate info for drone data sites

|
| Exploration |
|---|
| Site types |
| Guides |
Relic and data sites are types of cosmic signatures that can be found with probing. Data and relic sites can be divided to 4 categories:
- Pirate data and relic sites
- Drone data sites
- Ghost sites
- Sleeper caches
- Sleeper sites.
Contents
Pirate sites
Pirate relic and data sites can be found in all normal space regions, as well as in C1, C2 and C3 class wormhole systems.
They follow a simple naming convention:
Data sites in high security space they are called "Local (Faction) (site)", in low "Regional (Faction) (site)" and in null "Central (Faction) (site)". Relic sites in high security space they are called "Crumbling (Faction) (site)", in low "Decayed (Faction) (site)" and in null "Ruined (Faction) (site)". Each region spawns sites for the local pirate group.
Pirate relic and data sites are pockets of space populated with a variety of cosmetic structures (i.e., wrecked stations, abandoned machines) and several containers that need to be hacked before the contents can be accessed. The sites do not have any triggers or NPC defenders.
Data site containers look a bit like an gyroscope, and typically have names like "(Faction) Info Shard" or "(Faction) Com Tower". Relic Site containers look like ancient shipwrecks and have names like "(Faction) Debris" or "(Faction) Rubble". These containers hold all of the site's valuables. You'll have to hack into the containers first by playing the hacking minigame. In order to attempt a hack, you’ll need to lock on to the container, fly within your hacking module range of it, and then use the correct module on it (Relic Analyzer in a Relic Site, Data Analyzer in a Data Site, or Integrated Aanalyzer for both). This will pop open a new window containing the hacking minigame. Failing the hack on same container twice will destroy the container. The explosion will not deal any damage.
Pirate relic sites contain T1 and T2 salvage materials, skillbooks and blueprint copies. Pirate data sites contain decryptors, datacores, skillbooks, blueprint copies and manufacturing materials. The contents vary by faction, for example, Sansha relic sites contain Intact Armor Plates for salvage.
Drone data sites
Drone data sites spawn in drone regions only. Drone data sites have two main differences from pirate data sites:
- Failing the hack twice in drone data site will not destroy the container. Instead there is a chance that failure spawns hostile frigates. These rogue drones can be easily handled by the drones of T1 explorer and do not pose serious threat. These frigates need to be destroyed before you can hack again.
- Drone data sites can escalate into another drone data site.
Drone data sites contain three hackable containers: Two High "Security Containment Facility" and one "Research and Development Laboratories". Most of the time the lone research container is empty but leaving it unhacked misses possibility for data site escalation.
Drone data sites contain drone components and blueprint copies for 'Integrated' and 'Augmented' drones. Each drone region drop blueprint copies for different racial drones: Kalevala Expanse and The Spire for Minmatar, Malpais and Oasa for Caldari, Etherium Reach and Perrigen Falls for Gallente and finally Outer Passage and Cobalt Edge for Amarr.
Sleeper caches
Sleeper caches are data sites with various triggers and dangers. They are significantly more difficult than pirate data sites. Sleeper caches spawn in normal space and do not spawn in wormholes even though the sleeper connection would imply the opposite.
The Sleeper Caches from easiest to hardest are:
Sleeper caches are gated deadspace pockets with size limits for entry. Each sleeper cache has its own set of dangers. They contain mixture of containers with damaging explosions on failed hack, timed triggers, hazardous clouds, proximity explosions and sentry guns. For details see the page for individual sleeper cache.
Sleeper caches contain sleeper components, manufacturing materials, skillbooks and blueprint copies for polarized weapons.
Ghost sites
- Main article: Ghost Site
Ghost sites are data sites with limited time and riskier failures. They can be identified from "Covert Research Facility" on their name.
The sites have invisible time limit after which strong NPC force will arrive, blow up remaining containers and attack the pilot on site. The hacks are also riskier as single failure will cause the container to explode dealing 4000–6000 raw explosive damage to 10 km radius.
Ghost sites contain covert research Tools, villard wheels and bluepring copies for 'Packrat' and 'Magpie' mobile tractor units, ‘Wetu’ and ‘Yurt’ mobile depots and ascendancy implants, ,
Sleeper sites
- Main article: Wormhole sites
Sleeper data and relic sites are found in wormholes. They are not empty, instead they have strong sleepers defending the site that need to be defeated before hacking.
Sleeper data and relic sites can be identified from "Forgotten" and "Unsecured" at the beginning of their names. The combat in them is harder than in combat anomalies of same wormhole class and the rats drop sleeper components as they do in combat sites. They can be ran as combat sites only looting the wrecks and ignoring the hacking part.
Contested Covert Research Facilities
The only known variant is the Contested Guristas Covert Research Facility. It contains 1 hackable can, called a Guristas Transponder Tower. If the hack fails or after about 45-60s from the first warp-in to the site (even if the can has already been emptied), the can explodes for roughly 2000 raw explosive damage. The tower has 1 Guristas Data Sequence (eve-central price) as loot, 75/200/700 of which can be turned in at the Mordu's Legion headquarters in nullsec for BPCs to build the Mordu's Legion ships.
Even an exploration frigate (Magnate, Heron, Imicus or Probe) can be fitted to survive this with 2-3 cheap T1/meta tanking modules swapped into the regular exploration fit: for example, on the Imicus/Heron/Probe using this wiki's basic exploration/scanning fits, one could:
- keep 1 analyzer and the microwarpdrive in the mid slots,
- remove the other analyzer and the cargo scanner/rangefinding array (and optionally the Heron's 5th slot, but this isn't even really necessary, the Heron has/ends up with the largest shield tank anyway)
- add a small shield extender and a explosive deflection field (add a 2nd explosive deflection field on the Heron if you want)
- change 1 lowslot module (usually speed/align modules on exploration ships) for a damage control if the fit doesn't have one yet.
These modules take up only 10-15m³ in your cargo hold and can be fitted in at any nearby station whenever you come across a contested covert research site while exploring, and back out once you've done the site.
With a Magnate using the "exploration basic" fitting, just switching the drone damage amplifier to an armor explosive hardener should be enough, thanks to the 100mm reinforced plates, damage control and energized adaptive nano membrane already included in the fit. After fitting the armor explosive hardener, the EANM isn't necessary anymore to prevent the 2k damage from spilling over into structure hp, so the EANM can be swapped for a small armor repairer if you don't want to pay to repair your armor, but you may run into lack of power grid with low/mediocre fitting skills. In any case, the limited mid slots and low base shield hp of the Magnate make pure shield tanking impossible while keeping both the microwarpdrive and an analyzer, compared to the extra low available for armor tanking.
Note: The author of this section did model all 4 frigates in EFT, using a damage control I + explosive deflection field I + small shield extender I (except for the Magnate, as noted) and with the "without skills" option, and got just over 2k (Imicus) to 2.7k (Heron with 1 EDF) shield ehp vs. explosive damage on all the above ships except the armor-tanked magnate (which had about 2.5k shield+armor ehp vs. explosive, with AEH+100mm plates+DC+EANM). However, TEST YOUR OWN FIT with a fitting tool and/or calculate your EHP vs. explosive damage before you go blow yourself up. Remember to repair any armor/hull damage you may have suffered afterwards (as noted, this should only be necessary with the Magnate).
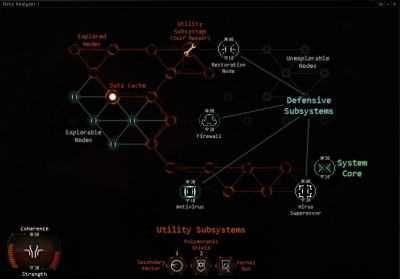
Hacking
Mercifully, the hacking minigame is identical in both Data and Relic Sites, aside from a few cosmetic changes to the game’s playfield and sound effects. The object of the hacking minigame is to find and disable the container’s System Core. You do this by maneuvering a virus through the board of “nodes” that represent the container’s electronics.
Moving around the board is easy enough. Unexplored nodes in the system are marked as green. Clicking on an unexplored node will reveal its contents: if the node is empty, it will turn orange and allow you to further explore nodes adjacent to it. Sometimes, however, a node will contain an obstacle or other item of interest.
Additionally, as you click on each node, if it is unoccupied (or after you clear the item from the node), it will briefly display a "minesweeper" number, from 1 to 5, which indicates the distance from the nearest non-empy node (5 means "5 or more".). This shows distance from any undiscovered Utility Subsystem, System Core, or Data Cache. The numbers can be used to guide the direction that you should move around the grid.
Among the various things a node may contain are...
Defensive Subsystems
These are represented by large circles with an icon inside, and they will be the bane of your hacking existence. Defensive Subsystems prevent you from exploring adjacent nodes until they are disabled. Each Defensive Subsystem has two ratings: Coherence represented by an asterisk atop the Subsystem, which is the equivalent of its health/HP, and Strength represented by a “wifi/signal” icon listed at the bottom of the Subsystem, which is equivalent to its “attack power.”
Your virus has a Coherence and Strength, too, which you can use to disable the system’s defenses! Your virus’s Coherence and Strength are listed in the bottom left of the hacking window. You can attack a Defensive Subsystem by clicking it after it has been explored. Attacking a Subsystem is turn-based: your virus will attack the Subsystem lowering the subsystem's Coherence by your Virus Strength, and then, if the Subsystem is still active, it will attack your virus back. If you reduce the subsystem's Coherence to 0, it is disabled and removed from the board.
If your Virus Coherence reaches 0, you fail the hack and the window is closed. Failing a hack once does not matter for regular Data/Relic sites, but failing a second hack will destroy that container. (Note that for some special kinds of containers/sites, such as Ghost Sites, Sleeper Caches, etc., failing the first hack might cause an explosion, or have other negative effects.). Interrupting a hack counts as a failure, and that includes moving too far away from the can (out of range of your analyzer) while the hacking window is open. This is sometimes a problem for frigates with a MicroWarpDrive active, where you can overshoot the can when Approaching it too fast - so be careful.
- Defensive Subsystems come in a few different types.
- Firewalls have high coherence, but low strength.
- Anti-Virus subsystems have low coherence, but high strength.
- Restoration Nodes show up in more difficult hacks. Each turn they are active, they will give extra coherence to all other uncovered defensive subsystems. Incredibly nasty.
- Virus Suppressor subsystems lower your Virus Strength while active.
System Core
The System Core operates a lot like a Defensive Subsystem, with the major difference that disabling it will successfully complete the hack. Its icon looks like a “><” inside a Subsystem circle.
- The color of the System Core reflects the difficulty of the container: Green for easy; Orange for medium; Red for hard.
Data Caches
Data Caches act a bit like a “treasure chest.” They can contain either a “treasure” (a useful Utility Subsystem), or a “trap” (a particularly nasty Defensive Subsystem). Data Caches have to be manually opened after being exposed (single-click them), so you can safely leave the decision as to whether or not to chance their activation until later on in your hacking attempt.
Utility Subsystem
Utility Subsystems are helpful, consumable “files” that have been left inside the system. You can click one once it has been exposed to add it to a utility slot at the bottom middle of your hacking window. They can then be used by clicking the appropriate utility slot. You can only store three Utility Subsystems at a time, so plan ahead!
- Utility Subsystems are extremely useful and come in a few different types.
- Self Repair utilities increase your Virus Coherence by a variable amount. A single Self Repair has three “charges”: the first is consumed immediately after use, and the next two are automatically used after your next two actions in the system (i.e., exploring a node, attacking a subsystem). Always use a Self Repair as soon as you find it - there is no gain in waiting.
- Kernel Rot utilities reduces a target subsystem’s Coherence by 50%. Great for use on the System Core. Useful too on defensive subsystems with high Coherence.
- Secondary Vector utilities reduces a target’s Coherence by a variable amount. Much like the Self Repair utility, the Secondary Vector has three charges: one used immediately, and two more that fire off after taking actions.
- Polymorphic Shield utilities prevent the next two instances of damage done to your virus. Good for taking down subsystems with high Strength.
Thankfully, exploring until you find the System Core and then annihilating it isn’t too difficult in the vast majority of sites you will find in high-sec. With a little practice, you’ll be hacking with the best of them!
Hacking Tips and Tricks
- As a general rule, you’ll want to explore as many nodes as you can before attacking any static Defensive Subsystems. In general, it’s better to explore the entire board before engaging with any subsystems: you may just stumble onto the System Core early! Restoration Nodes and Virus Suppressors are the exception to this though, as they should be removed from the board as soon as possible.
- Always pick up Utility Subsystems as soon as they are exposed. If you keep exploring without snagging these, a Defensive Subsystem might pop up and cut off your access to them!
- Always use a Self Repair as soon as you find it. It simply increases your Coherence, so there is no gain in waiting.
- Don’t open Data Caches until you’ve fully explored all their adjacent nodes. You don’t want your exploration to be cut off by an unexpected Defensive Subsystem!
- Additionally, more difficult hacks contain Data Caches that might expose particularly nasty Defensive Subsystems (Restoration Nodes), so sometimes, you may just want to leave opening Data Caches as a last resort.
- Because exposed Defensive Subsystems cut off access to adjacent nodes, you may want to explore nodes along the edges first before exploring inward. This is because if you happen to expose a Firewall or Anti-Virus along a “wall,” you will be a bit less likely to cut off all of your movement options in that direction.
- Use the 1-5 "minesweeper" numbers to guide your movement around the grid. For example, if you're approaching an edge or corner of the grid, and the number is a 5, then trying to explore anything towards that corner/edge is not useful, because you know that there cannot be anything good within 5 nodes. In general, you want to click in directions that make the numbers smaller. Because the numbers disappear as you move along, you need to remember where there were 5's, so you know which areas not to bother going back to later.
General tips and tricks
- The contents of containers can be scanned with cargo scanners before hacking. This allows skipping containers that do not have valuable contents.
- Emptied sites will despawn in few minutes. Sites that have been warped to or partially completed will despawn in few hours.